As part of its daily operations, Buna collects different types of data and information, including the personal information of its personnel, market participant, and Financial Holding Institution (FHI) representatives, as well as transaction data that shall be settled through the system. Buna upholds the highest standards of data privacy, and as such enforces a data privacy policy diligently while carefully storing and protecting the data it collects.
The collected data and information are used to deliver Buna’s services, monitor transactions for Anti-Money Laundering and Combatting the Financing of Terrorism (AML/CFT) purposes, fulfill legal obligations, provide access to its systems and generate statistical reports.


Access to data is primarily focused to ensure the proper delivery of services and safe operations of the overall system.
Buna’s team has highly restricted access to data; Only selected roles are allowed to access transaction data when necessary.
Participants have full access to their own data through the portal and reports.
Overseeing authorities have access to transaction data and reports to manage and monitor currency usage, supervise payment flows, and discharge statutory authority.
The general public has access to statistical and industry reports disclosed by Buna.
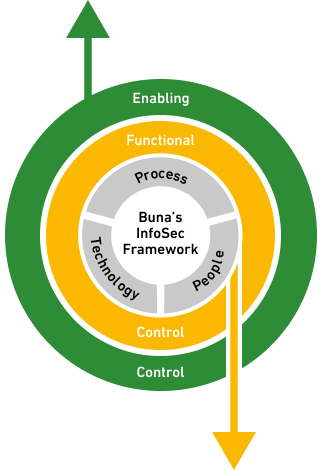
Buna’s information security programme is built on a comprehensive framework and represent an upmost priority by complying with international information security standard and accreditation, such as ISO 27001-2022 and SWIFT CSP (Customer Security Programme), and putting in place additional preventative measures to protect the organization from information security breaches and cyberattacks.
Through a multi-layered security approach, Buna protects its digital assets from unauthorized access and use and processes payment transactions through each layer of infrastructure safely by relying on different cryptographic methodologies. bili